This article was slated for a later release, but given the news about nearly 200 million American’s PII was made publicly available by a firm working for the RNC, we have decided to release this early.
[More information can be found here: http://gizmodo.com/gop-data-firm-accidentally-leaks-personal-details-of-ne-1796211612]
At the time of writing this article, 1,941 total breaches that have affected more than 500 people in a single incident have been reported to the Department of Health and Human Services since its inception in 2009. Yet there are thousands of organizations that are HIPAA compliant. How does this happen? Here is a little unknown secret. Compliance is not the same as Risk Management. Moving beyond HIPAA is where we find ourselves today: in need of a solution that requires active vigilance to protect your most valuable asset — your data.
Here’s some of the raw data with you that will help frame the rest of our research and solutions:
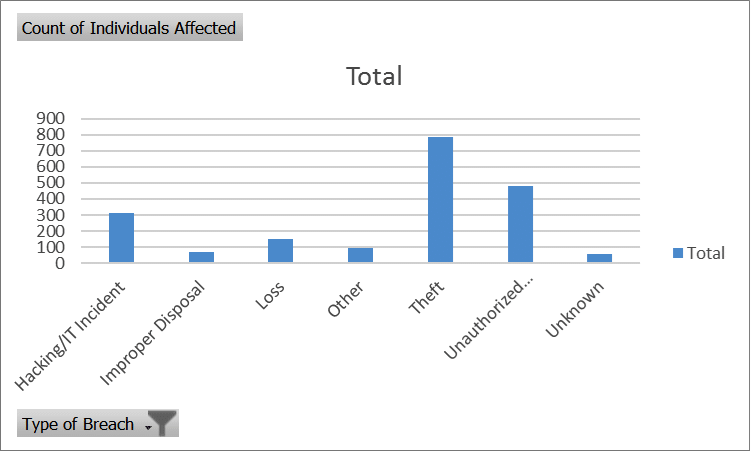
As you can see, most breaches occur through theft and unauthorized access to protected systems that contain electronic protected health information (ePHI), or electronic heath records (EHR). Your own employees are the largest culprits of this happening, sometimes with non-malicious intent. It is simply because they don’t know any better, or proper risk measurement and employee training has not taken place. A more sobering chart is below.

More than 130,000,000 people have been affected by hacking and/or an IT incident. The total number of Hacking incidents is only 40% of the total number of breaches by Theft, however Hacking represents a 500% increase in the total number of effected individuals. Please keep in mind, this is not the total number of incidents that have occurred. I can assure you incidents happen every day that go unreported. And to put into perspective just how vulnerable these companies are, only 10 organizations accounted for nearly 93% of that 130 million affected consumers.
Organizations are having to adopt a more proactive approach towards data security and risk management. HIPAA was created in 1996 in order to combat the improper use of healthcare patient data. It is a set of compliance rules that many organizations are required to adopt if they are going to maintain patient data, in any form. Yet in these sophisticated times where attack vectors and hacking methods are much more mature and advanced, compliance is not enough. This has given rise to organizations such as the Health Information Trust Alliance, or HiTRUST, which will be the topic of our next post.
As always, if you think you are at risk, or anticipate that you might be out of compliance and face penalties because of it, here at TechCXO we have partners in our Product and Technology practice that specialize in assisting customers get and maintain their certifications. We have worked directly with the HiTRUST counsel on numerous engagements and would welcome a conversation with you in order to ensure that you are meeting your compliance requirements and put forth a plan of action that will ensure every possible protection option has been explored.
What does this mean for you today? It is time to take action…right now. If you don’t know the state of your security and are reading this article right now, you should know. Here are threeo steps to take immediately:
- Contact your security services provider, either internal or external, and have them run a full audit and scan of your systems, both internal or cloud based systems for potential holes in your perimeter security.
- Schedule time with your teams to look at potential areas where PII, ePHI, or any other protected information may exist and have them immediately evaluate those potential ingress and egress access points for proper security implementations.
- If you don’t have a security services provider, contact us here at TechCXO and we can assist you in locating one or engage you directly in order to quickly give you peace of mind.



